Why is cloud security important?
With cyber criminals constantly on the hunt for anything that they can steal and sell, exploit or hold for ransom, security is a primary concern for all modern businesses. From small businesses to the largest of organisations, anyone can be a target.
Whether it’s distributed denial of service (DDoS), malware, SQL injection or data breaches, all attacks can have financial repercussions and significantly impact the reputation of a business. In most cases, however, these breaches happen due to a lackluster approach to cloud security.
In this guide, we’ll cover best practices for multi-layered cloud security management and how security experts can help support safe functionality when building, deploying, and managing cloud-based applications.
What is cloud security?
The goal of cloud security is to protect your cloud-based systems, data, and infrastructure against both internal and external threats. This is done by the use of technologies, controls, processes, and policies – all working together in tandem.
Top 5 cloud security challenges
Let’s take a look at the most frequent challenges IT teams face when it comes to cloud management:
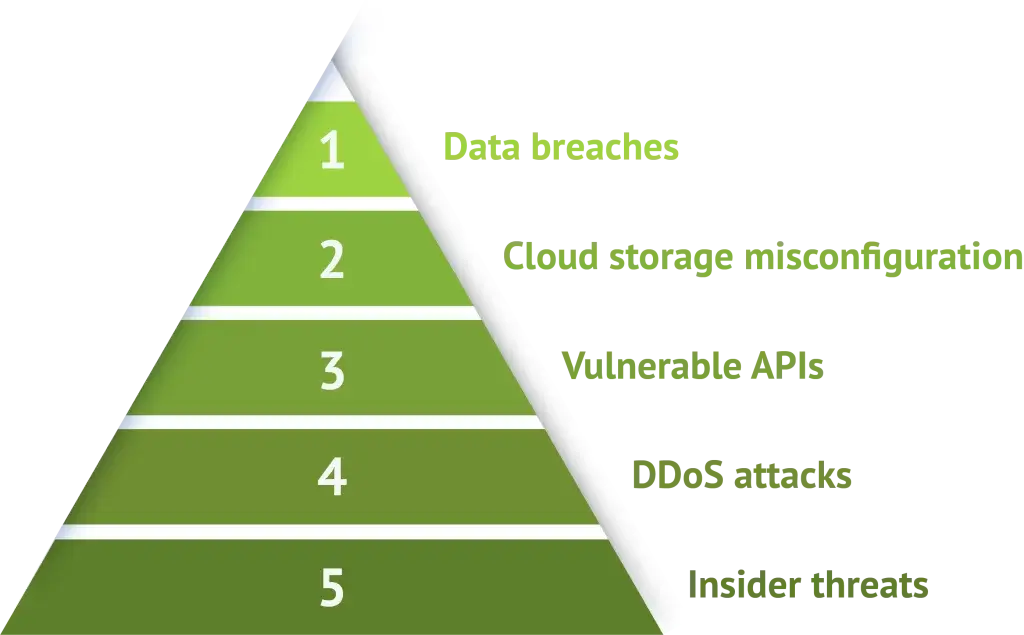
Data breaches
Cloud infrastructure that is not secured sufficiently can result in the loss of sensitive corporate information, which could disrupt your business for many days or even weeks. A data breach can also damage your business reputation, and potentially even have legal consequences if it is found the breach was caused by your business incorrectly handling data. Around 60% of companies that experience a critical data breach go out of business six months after the incident.
Сloud storage misconfiguration
Shockingly, misconfigured cloud storage services are commonplace in 93% of deployments accounting for regular sources of stolen data. Hackers have many ways of exploiting misconfigured cloud environments, so proper access management and expertise are essential to prevent data leakage.
Vulnerable APIs
Cloud service providers commonly use APIs as a way for customers to access and extract information from their cloud-based services. However, if these APIs are not configured properly with sufficient authentication controls, they can be exploited and leak sensitive information to hackers.
Insider threats
Employees can pose even more of a danger to cloud security than outside attackers, often down to a lack of training or negligence. Your platform can use the top security measures, but if an employee clicks a phishing link in an email, or leaves an unlocked laptop in a public place, your business is at risk. Business partners, contractors, or anyone who has had access to systems in the past could also be considered an insider threat if they intentionally abuse their access permissions.
DDoS attacks
DDoS attacks can prevent users from accessing mission-critical data and applications, causing significant or even irreparable financial damage to the business. With cloud environments a longstanding target for DDoS attacks, regular cloud security assessments are vital.

Cloud security best practice
Cloud security management is about understanding the security controls you have in place to secure your environment, systems, and data. Managing security for cloud infrastructure can be simpler than traditional on-premise infrastructure. Many elements can be automated, instead of relying on human workloads or trial-and-error.
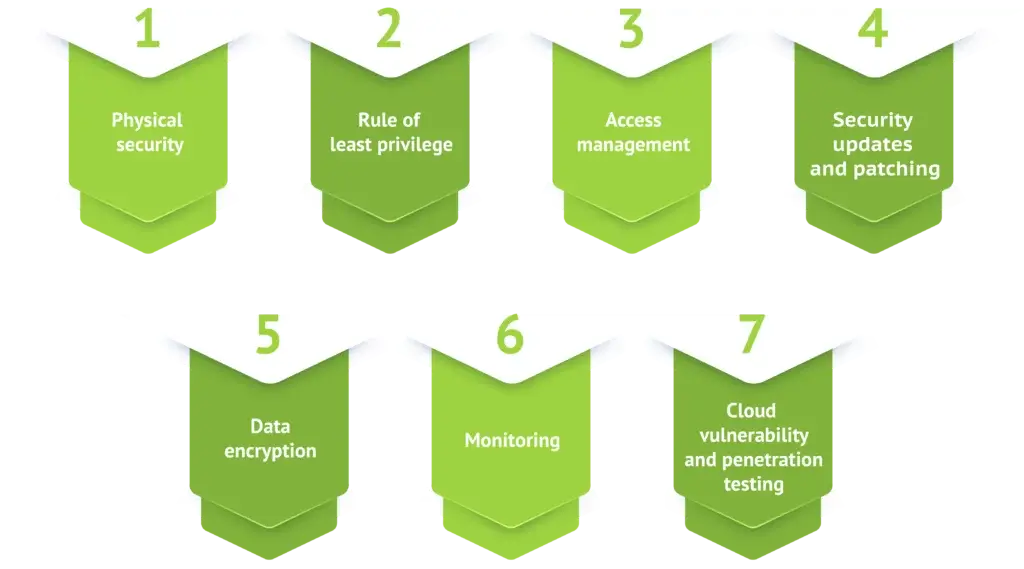
Physical security
Your cloud provider is responsible for the physical security of your infrastructure, which involves a combination of measures to prevent disruption of hardware housed in the data centre. Stringent physical security measures can include 24/7 CCTV, biometric scanners, card readers, video monitors, and mantraps to prevent unauthorised access.
Rule of least privilege
Whether you’re talking about cloud, on-premises or even a desktop computer running in your office, you should always implement the rule of least privilege. If a system doesn’t need to do something, don’t allow it to. For example, if you have a server that’s only used for processing information in a SQL database, don’t install a web browser. This eliminates the number of ways bad actors can get in or out.
Access management
Put simply, if a person within your organisation doesn’t need access, don’t give it to them. Take a zero-trust approach both inside and outside your organisation, where you choose to trust nothing and nobody. Users should only have access to the minimum information that they need. Then, if an account gets compromised, the attackers do not have access to the whole system. Proper access management makes it very difficult for anyone to do something they shouldn’t be doing.
Security updates and patching
In order to maintain a secure cloud environment, your security systems must always be up-to-date. Without doing these critical updates, almost anyone can get into your system and compromise it – often using free, open-source tools online. In fact, around 60% of breaches were caused by unpathed software, most of which had been ignored for years.
Data encryption
When you use cloud technology, you are sending data to and from a cloud provider’s platform, often storing it within their infrastructure. Encryption is another layer of cloud security to protect your data, by encoding it when in transit as well as at rest. This means that the data is practically impossible to decipher without a decryption key that only you have access to.
Monitoring
Cloud monitoring is a method of observing and managing the operational workflow in a cloud-based IT infrastructure. By using advanced monitoring tools, like IDS and IPS, to identify any attack, misuse or malfunction of the service, you or your cloud provider can take quick and decisive action to address any incident.
Related Content: How Intrusion Detection Systems and Intrusion Prevention Systems
Cloud vulnerability and penetration testing
Performing vulnerability and penetration testing is another way to secure your cloud environment. These practices usually involve attacking your own cloud infrastructure to identify any potential weaknesses or exploits. You can then implement solutions to patch any vulnerabilities that are highlighted.
Related Content: Learn more about cloud security from one of our experts
Protecting your infrastructure from physical threats
Hosting infrastructure consists of physical hardware located in data centres globally, which can be vulnerable to risks we might not consider. As a business, it is vital to be aware of these risks and take preventative measures.
Supply chain disruption
The physical hosting infrastructure housed in data centres includes various hardware elements. The core components are servers, arranged in racks and stacked in server rooms, storage systems connected to the servers to store and manage data, and networking equipment such as routers, load balancers and firewalls.
An effective strategy to protect against supply chain disruption is supply chain mapping. All points of the chain are identified, and any potential chokepoints or vulnerabilities are analysed to inform a risk mitigation strategy.
Environmental factors
As hosting infrastructure is housed in physical data centres, it is vulnerable to environmental factors. Internet traffic is directed around the world using undersea cables, and satellites, which are similarly vulnerable.
Natural disasters, including earthquakes, hurricanes and floods can damage both data centres and internet transmission infrastructure. Extreme weather can cause damage, for example a heatwave which a data centre does not have sufficient cooling systems to manage, or a storm damaging undersea cables. Satellites can sustain environmental damage through collisions with debris, or excess radiation.
To protect against environmental disasters, data centres can employ precautionary measures. This can include seismic bracing for earthquake protection, flood barriers, fireproofing, and temperature control. When selecting and working with a cloud provider, businesses should discuss with the provider what measures they use.
Physical security threats
We frequently discuss cybersecurity threats such as ransomware or phishing, which exploit weaknesses in software or human error. Physical security threats are considered less often, but can pose significant risk to internet infrastructure.
With regards to physical security, your hosting provider can minimise the risk to your platform. Your provider should equip their data centres with physical security measures. This can include intrusion prevention and detection systems, controlled access, and security staff. This will prevent any unauthorised access putting your hosting infrastructure at risk.
To Learn more about protecting your infrastructure from physical threats check out the below resource.
Related content: Protect your business against the physical threats to your hosting architecture
Protecting against Ransomware
Ransomware attacks have been front and centre in recent news. Ransomware attacks increased by 68% in 2023, and the average ransom demand also increased. In 2024 over 46% of businesses, breached by a ransom attack, reported losing over a million dollars in damages.
All businesses must be prepared for a ransomware attack, and put in place measures to protect themselves. With many large names suffering attacks, it is clear it is not possible to completely prevent ransomware attacks. Businesses should have a plan in place to minimise impact on their business operations.
Find out about our Ransomware protection.
What is Ransomware?
Ransomware is a type of malware that prevents users from accessing files, either by encrypting them or locking them. The attackers then demand a ransom payment from the victim, promising to decrypt the files once the ransom has been paid.
Anyone can be a victim of a ransomware attack. Some attackers may target their victims based on opportunity, while others will target organisations that are likely to pay fast due to their reliance on files and data. For example,an estimated 45% of healthcare orgnaisations reported being targeted by ransomware attacks, with the attacker’s logic being that if lives are at risk the ransom is more likely to be paid. In the event of a ransomware attack, paying the demand does not guarantee that the encrypted files will be restored, and may lead to repeat attacks as the attacker knows they can succeed.
Ransomware attacks have many consequences including: temporary or permanent loss of important data, disruption to operations, financial loss and harm to a business’s reputation.
How to protect against ransomware
Due to the severity of the potential risk, it is crucial to prevent ransomware attacks. Two of the most effective ways to do so are with Anti-virus software and On and Off-site-backups.
At Hyve, we offer antivirus protection such as ESET and SOPHOS to prevent ransomware, as well as on and off site backups for added security.
Antivirus software
Hyve offers two types of antivirus software – either Sophos (typically used for Windows OS) or ESET. These types of software offer fast scanning and the highest rate of proactive detection. On detection of a threat (such as ransomware), the antivirus software will issue you with a warning, allowing you to avoid any incoming virus.
On and Off Site Backups
If your system is infected with ransomware, an on-site backup allows you to restore your data in a timely manner, ensuring minimal disruption to your business. We would recommend that your on-site backups back up your data once a day, with a seven-day retention period. For extra security we recommend can also offer off-site backups, meaning that your data will be backed up on site, as well as being backed up to another data centre for extra security.
Hyve offer customisable back-up intervals and if you require more regular backups or more than a seven-day retention period, this can be arranged. We can back up full virtual machines or you can opt to only back up certain files.
A well-planned backup solution ensures that in the case of a ransomware attack, you would be able to roll back to your latest backup and restoreyour vital data.
Rule of least privilege
Whether you’re talking about cloud, on-premises or even a desktop computer running in your office, you should always implement the rule of least privilege. If a system doesn’t need to do something, don’t allow it to. For example, if you have a server that’s only used for processing information in a SQL database, don’t install a web browser. This eliminates the number of ways bad actors can get in or out.
Access management
Put simply, if a person within your organisation doesn’t need access, don’t give it to them. Take a zero-trust approach both inside and outside your organisation, where you choose to trust nothing and nobody. Users should only have access to the minimum information that they need. Then, if an account gets compromised, the attackers do not have access to the whole system. Proper access management makes it very difficult for anyone to do something they shouldn’t be doing.
Security updates and patching
In order to maintain a secure cloud environment, your security systems must always be up-to-date. Without doing these critical updates, almost anyone can get into your system and compromise it – often using free, open-source tools online. In fact, around 60% of breaches were caused by unpathed software, most of which had been ignored for years.
Secure your network with a firewall
Firewalls are network security devices that monitor incoming and outgoing network traffic. They prevent unauthorised use of and access to your network by deciding which traffic to block or allow based on a set of rules. They act as the first line of defence in securing sensitive information online, providing a protective barrier against attacks.
Firewalls can be either hardware or software-based, with many companies choosing a combination of both. Software firewalls are installed on individual computers on a network and are configured with the operating system (OS). They protect individual computers against outside attempts to gain access can closely inspect data and block specific programs from sending data to the internet.
Hardware firewalls are physical devices that filter incoming and outgoing traffic for the entire network. They act as gatekeepers between the office network and the internet, with one or two devices used to protect the entire network. There are several different types of firewalls, including packet filtering firewalls, application-level gateways and web application firewalls (WAF).
Virtual Private Networks
Routing your connection through a irtual Private Network (VPN) t allows access to the internet in a safe and private way. This encrypted connection method adds a layer of security when connecting via a public network like a Wi-Fi hotspot.
VPNs are often used by businesses to protect sensitive information as they encrypt data. The VPN connects to the internet on your behalf, so that your private information is not exposed to potential risks or other people watching the network. The destination site sees the VPN as the traffic origin and not the individual user. No-one can identify you or your computer as the source of data, which websites you are visiting, or what kinds of information you are sharing.
There are two main types of VPN – client-to-site and site-to-site. A client-to-site VPN is an application that you connect to from your PC or laptop to securely access your files or browse the internet. This is a useful solution for anyone who needs to securely connect to their company network remotely or from a public place.
A site-to-site VPN is an encrypted VPN between your office network and the data centre. It works as a connection between your computer and the VPN server, protecting the data being transmitted.
SSLs for your website
Secure Sockets Layer (SSL) certificates are the standard security technology for an encrypted link between a web server and a browser.
The link ensures that all data that is passed between the web server and browsers remains private and secure. If a website doesn’t have an SSL certificate, a secure connection can’t be established. SSLs ensure that your website is secured and encrypts all sensitive information, such as usernames, passwords and any sensitive information. SSLs are vital for all websites for security reasons, but especially sites that take payment card information.
Google now penalises websites for not having SSL certificates and therefore not being secure and encrypted. Sites are flagged as ‘unsecure’ affecting the way that site visitors perceive the brand.
Traditional IT Security vs Cloud Security
Where traditional IT security manages access to systems via a perimeter security model, the cloud adopts a data-centric approach to prevent unauthorised access.
Cloud security can include data encryption and multi-factor authentication, making it a far more secure option.The cloud also offers the ability to automate backups on geographically diverse sites as part of a wider disaster recovery strategy. Traditional IT methods can make redundancy backups in multiple sites, but these tend to be far more costly.
With traditional IT infrastructures, if attackers have access to the network, they can threaten other resources too. But with a zero-trust approach – which is engrained in the cloud – attackers need to verify their identity in every step, making it more difficult to access important data.
Think of it in terms of getting into a multi-floor nightclub; with a traditional security approach, the bouncer checks your ID on the door and you can go anywhere. With a zero-trust approach, however, getting into the club is only the first check. The bartender must also check your ID before you can be served, regardless of where you are in the club.
Related Content: Read our insight on the difference between cloud security and traditional IT security?
Which cloud security certificates are best?

Security certificates and accreditations are an essential considerations when choosing a cloud provider. Working with a cloud provider with up-to-date security accreditations directly benefits your business, . It proves to your customers that your business is compliant, and it takes the stress of auditing out of your hands. There are many certificates you might be looking for based on your industry and the data regulations your business has to meet, however, there are some core accreditations that you should look for..
Essential security accreditations:
- ISO
- SOC 2 (if in the USA)
- Cyber Essentials
What is ISO?
The International Organisation for Standardization (ISO) is a non-profit organisation that develops International Standards. International Standards are documents that outline the benchmark for quality management and organisation in the workplace. While some International Standards are industry-specific, many are generic and can be implemented by any type of business.
What is SOC 2?
Developed by the American Institute of Certified Public Accountants (AICPA), SOC 2 is an auditing procedure designed for service providers that store customer data in the cloud to ensure that their information security measures are up to standard.
SOC 2 stands for “System and Organisation Controls” and is about putting well-defined policies, procedures, and practices in place and then testing them over a long period of time – not just ticking all the compliance checkboxes. Doing so effectively builds trust with customers and end-users about the secure nature and operation of our company and our cloud infrastructure.
Related Content: read our insight on ISO certifications
Related Content: read out insight on SOC 2
The human element of IT security
How employees are often the weakest link within a business
Falling for phishing scams
Email scams are the most common phishing attack that a company tends to encounter. Emails that appear to be from reliable sources are sent to employees with the intent of convincing them to download malicious software or hand over sensitive information.
According to a report by vpnAlert, Google and Facebook lost $100 million to a single phishing attack in 2 years. This staggering statistic should be enough to incentivise employers to put measures in place to reduce phishing scams.
Many workers believe that the necessary safeguards are in place to protect them from phishing attacks, yet hackers are always evolving. The technology of a company may not always be up to date with the increasingly sophisticated phishing assaults and link frauds. While employees may depend on the company’s IT security, ultimately they are the last line of defence and must be trained to identify the warning signals of a cyber assault.
Using the same password for multiple platforms
Companies use a number of resources to assist employees with general tasks including email, project management tools and accounting software. Password management doesn’t usually make the cut in the ‘basic tools package’ and is often a second thought.
Employees should be taught the fundamentals of password awareness, including how to create a unique, secure password, the importance of changing passwords regularly and the importance of using different passwords across platforms. Implementing a company password policy and introducing a password management tool, such as LastPass, can break the cycle of bad password habits.
Laziness and carelessness
Laziness and carelessness by employees can result in small mistakes with large consequences. Misdelivery of information, failure to keep software updated and incautious use of public networks can all increase vulnerability to cyber assaults. With an increase in remote work, employee awareness is crucial to ensure cyber safety whilst working from remote locations without direct oversight of IT support teams.
What is a social engineering attack?
Social engineering attack techniques are fast becoming one of the most popular ways for cyber criminals to ‘get inside’ an organisation.
In a social engineering attack, hackers gain access to sensitive business information by playing on human psychology and emotion reasoning and error rather than using technical skills to attack the business. A common social engineering attack that most people are familiar with is phishing. This can take the form of an email with an infected attachment, a message from a fake social media account asking for sensitive information, or a targeted ‘spear phishing’ email, where the message is tailored to the recipient.
Other social engineering attacks include voice phishing (more recently using AI generated audio), pretexting, and baiting – new threats are continually being developed and cyber security awareness training is essential to keep up.
Find out how to protect against social engineering in our awareness training section.
What can you do as an employee to stay secure?
Completing quick and simple safety checks prior to installing applications and programmes can reduce the risks involved. This should include:
Double-check the website address
Look for either HTTPS at the beginning of the address or a lock symbol. These sites are secured through SSL/TLS encryption and have a certificate to prove this. Take another look at the domain to ensure it is the site that you think it is.
Use active virus and malware scanners
This software can scan files before installation and prevent you from downloading files that contain viruses and malware.
Awareness training
Having untrained employees in the workplace is a risk to cyber security. The rise in these types of attacks shows how important awareness training is, and reinforces the need for businesses to create a culture of cyber security in the workplace. Effective and memorable cyber security training focuses on real world examples and situations that employees can relate to, rather than endless PowerPoint slides. Help your employees understand why they are an attractive target for cyber attackers and how to detect suspicious activity.
Training needs to be carried out regularly, especially as new threats arise. Employees can also be tested on their knowledge as well as being sent fake phishing emails in order to test the success of the awareness training.
Cyber security 101
Every business needs a cyber security strategy and awareness training scheme that is regularly updated. This should create a culture of cyber security in the workplace that makes employees intuitive and hyper-aware of any potential threats to security.

Cyber Security 101 diagram
Even the most simple measures will help to protect online security:
- Continuous training – Keep employees up-to-date with all the latest security threats and how to react in certain situations.
- Review processes – Review existing processes, procedures and controls in the business often. Ensure that incident management and reporting systems are always tested. User accounts, privileges and permissions should also be regularly monitored.
- Multi-Factor authentication – Using multi-factor authentication means that the additional steps of security makes it so much more difficult for a hacker to break into online accounts. Use VPNs, SMS based authentication, app-based authentication, biometrics or YubiKeys for accessing sensitive company data.
- Emails and attachments – All businesses should have strict policies that state that links and attachments received in emails should not be clicked on or opened. Anything that looks suspicious should be treated with caution. Awareness training should prepare employees for cross-checking and confirming news with other people if they were to receive a spear phishing email.
- Passwords – We’ve all been told a thousand times, but password management really is a necessity when it comes to online security. Don’t use default passwords and use strong and secure passwords or a password manager.
- Firewalls – Use a firewall to block any unauthorised access to computers or networks.
- Anti-virus software & system updates – Anti-virus software should be running constantly and reports should be taken to ensure that computers or equipment in use are not a threat. Always ensure that patches and updates are made to all computers.
Every business should create a culture of cyber security. The best line of defence against social engineering attacks is user education and layers of defence that detect and respond to attacks.
Insights related to Content Hub

Get in touch